Universal Cloud Service - Streamline Your Workflow Internationally
Universal Cloud Service - Streamline Your Workflow Internationally
Blog Article
Utilize Cloud Provider for Enhanced Information Safety And Security
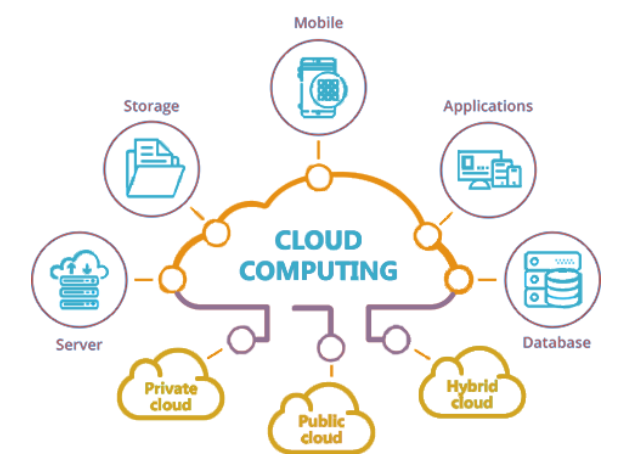
In today's digital landscape, the ever-evolving nature of cyber dangers requires a positive technique in the direction of guarding delicate information. Leveraging cloud solutions offers an engaging remedy for organizations looking for to strengthen their information safety actions. By handing over trusted cloud provider with data monitoring, organizations can use a wide range of safety functions and sophisticated modern technologies that strengthen their defenses versus destructive stars. The concern arises: how can the utilization of cloud services revolutionize data security practices and provide a robust shield versus possible vulnerabilities?
Value of Cloud Safety
Guaranteeing robust cloud safety procedures is critical in securing delicate data in today's digital landscape. As companies progressively depend on cloud solutions to store and refine their data, the demand for solid protection methods can not be overstated. A violation in cloud safety and security can have extreme repercussions, ranging from economic losses to reputational damage.
One of the key reasons cloud safety is vital is the common responsibility design used by many cloud provider. While the provider is in charge of safeguarding the facilities, consumers are liable for safeguarding their information within the cloud. This department of obligations highlights the importance of applying durable safety and security measures at the individual level.
In addition, with the expansion of cyber hazards targeting cloud settings, such as ransomware and data breaches, organizations need to stay vigilant and positive in mitigating threats. This entails frequently updating protection methods, monitoring for suspicious activities, and informing workers on finest methods for cloud protection. By focusing on cloud protection, companies can much better shield their delicate data and maintain the trust of their customers and stakeholders.
Data Encryption in the Cloud

File encryption in the cloud normally entails using cryptographic algorithms to rush information into unreadable formats. This encrypted data can just be deciphered with the matching decryption trick, which includes an added layer of safety and security. In addition, numerous cloud provider provide file encryption devices to safeguard data at remainder and en route, enhancing general information protection. Implementing durable security practices alongside other safety and security procedures can significantly bolster a company's protection versus cyber hazards and safeguard valuable information stored in the cloud.
Secure Information Back-up Solutions
Information backup services play an important duty in making certain the strength and safety of data in case of unanticipated cases or data loss. Secure data backup services are important parts of a durable information security approach. By consistently supporting data to safeguard cloud servers, organizations can alleviate the dangers associated with information loss because of cyber-attacks, hardware failings, or human error.
Executing protected data backup remedies includes choosing dependable cloud company that provide file encryption, redundancy, and information integrity actions. File encryption ensures check that that information remains safe both en route and at remainder, protecting it from unapproved access. Redundancy devices such as data replication throughout geographically dispersed servers aid avoid full data loss in situation of web server failures or all-natural calamities. Furthermore, information integrity checks ensure that the backed-up information remains tamper-proof and unaltered.
Organizations should establish automatic back-up schedules to make sure that information is consistently and effectively supported without manual intervention. Normal testing of data reconstruction processes is likewise critical to guarantee the effectiveness of the back-up solutions in recovering data when required. By purchasing safe information backup solutions, organizations can enhance their information safety pose and reduce the impact of possible information breaches or interruptions.
Role of Accessibility Controls
Applying rigid gain access to controls is vital for preserving the security and honesty of delicate information within business systems. Accessibility controls function as an important layer of protection against unapproved accessibility, guaranteeing that only accredited people can check out or control delicate data. By specifying that can gain access to details sources, companies can limit the threat of data violations and unauthorized disclosures.
Routinely evaluating and updating access controls is vital to adapt to business modifications and developing security hazards. Constant monitoring and bookkeeping of gain access to logs can assist detect any kind of questionable activities and unapproved gain access to efforts immediately. Overall, durable accessibility controls are essential in protecting delicate information and mitigating security dangers within business systems.
Conformity and Laws
On a regular basis guaranteeing conformity with pertinent policies and criteria is important for organizations to promote data security and privacy measures. In the realm of cloud services, where information is usually kept and refined on the surface, adherence to industry-specific regulations such as GDPR, HIPAA, or PCI DSS is essential. linkdaddy cloud services.
Cloud service suppliers play a crucial function in helping organizations with conformity initiatives by supplying solutions and attributes that line up with different regulative demands. As an example, numerous suppliers use file encryption abilities, gain access to controls, and audit tracks to assist organizations meet data safety standards. In addition, some cloud solutions go through routine third-party audits and certifications to demonstrate their adherence to industry regulations, providing added guarantee to companies seeking certified options. By leveraging compliant cloud solutions, companies can enhance their data safety and security posture while fulfilling governing commitments.
Conclusion
To conclude, leveraging cloud services for improved data safety is vital for organizations to shield sensitive details from unauthorized access and prospective breaches. By implementing robust cloud security procedures, consisting of data encryption, their explanation safe backup options, gain access to controls, and compliance with laws, companies can gain from advanced protection measures and experience provided by cloud service suppliers. This helps reduce threats efficiently and makes certain the confidentiality, integrity, and accessibility of data.

Data back-up remedies play a vital function in making sure the durability and security of information in the event of unexpected cases or data loss. By routinely backing up information to protect cloud servers, companies can reduce the risks connected with data loss due to cyber-attacks, equipment failures, or human error.
Implementing safe data backup solutions includes choosing trusted cloud solution companies that offer file encryption, redundancy, and data honesty steps. By investing in secure information backup options, services can enhance their information safety posture and reduce the influence of prospective information breaches or interruptions.
Report this page